Whoever works with Linux servers on the web knows it, logs filled with attempted accesses, brutforcers or simply spambots. Fortunately there are some sites that have specialized in collecting these "bad IPs" via honeypots or logging reports.
I use a small custom BASH script to load these IPs directly into my server iptables firewall. This list contains an average of 2500 entries from individual IPs /32 or partly whole networks up to /18. This script loads two lists every night, one with the most active hosts of the last 2 weeks from badips.com and the global DROP Hammer (Do NOT Route Or Peer) from emergingthreats.net. Both combined then pass through a sorting and filtering process in order to finally refuse any Connects from those IPs in iptables directly with DROP.
You can get the whole Script in this GIST, feel free to use.
To use it, you need those Packages installed: wget, egrep, iptables All of it should be installed on any normal Linux based Distri.
To install just save the Script to your server e.g. in /opt/badipblock.sh give it chmod +x and add a cronjob:
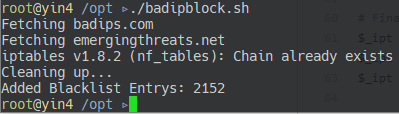
33 3 * * * /opt/badipblock.sh >/dev/null 2>/dev/null Running the Script will result in something like this:
I do recommend to use iptables-persistent package to save the state of your iptables. But be sure not to save after the blocklist is in the tables, save before so after a reboot your system comes up without blacklist.


Comments